A closer look at the Angler exploit kit – Sophos News
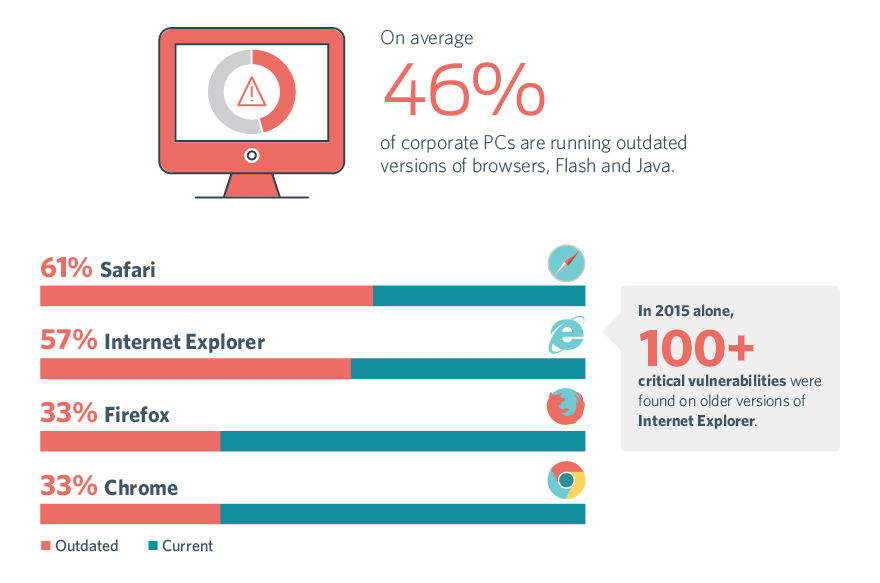
Flash Vulnerabilities & Exploits: An Information Security Primer
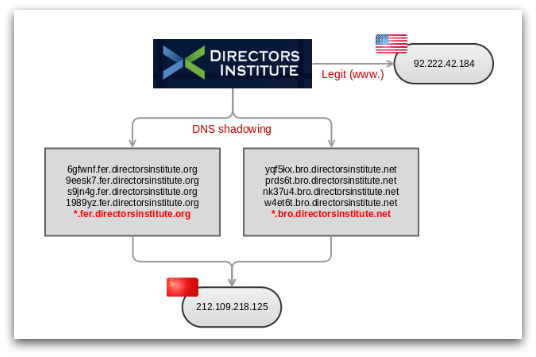
Cisco Talos Intelligence Group - Comprehensive Threat Intelligence

SOPHOS presentation used during the SWITCHPOINT NV/SA Quarterly
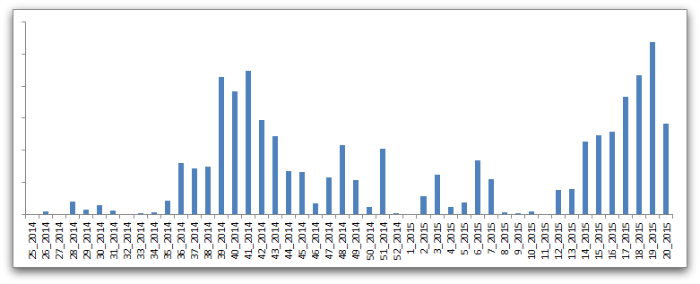
Angler Exploit Kit - Operating at the Cutting Edge

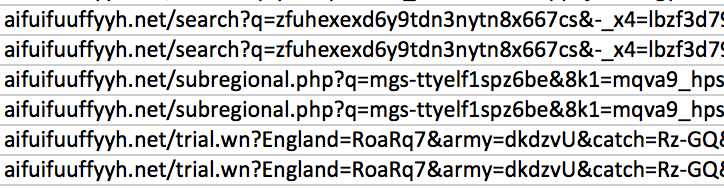
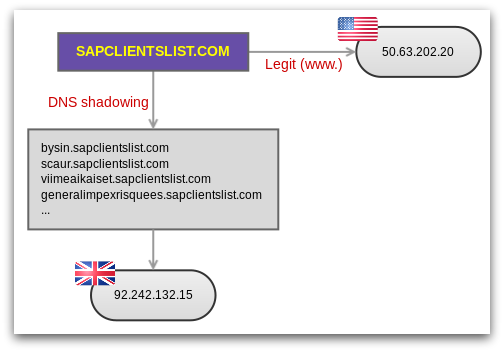
The shadow knows: Malvertising campaigns use domain shadowing to
A closer look at the Angler exploit kit – Sophos News

Flash zero-day monster Angler dominates exploit kit crime market
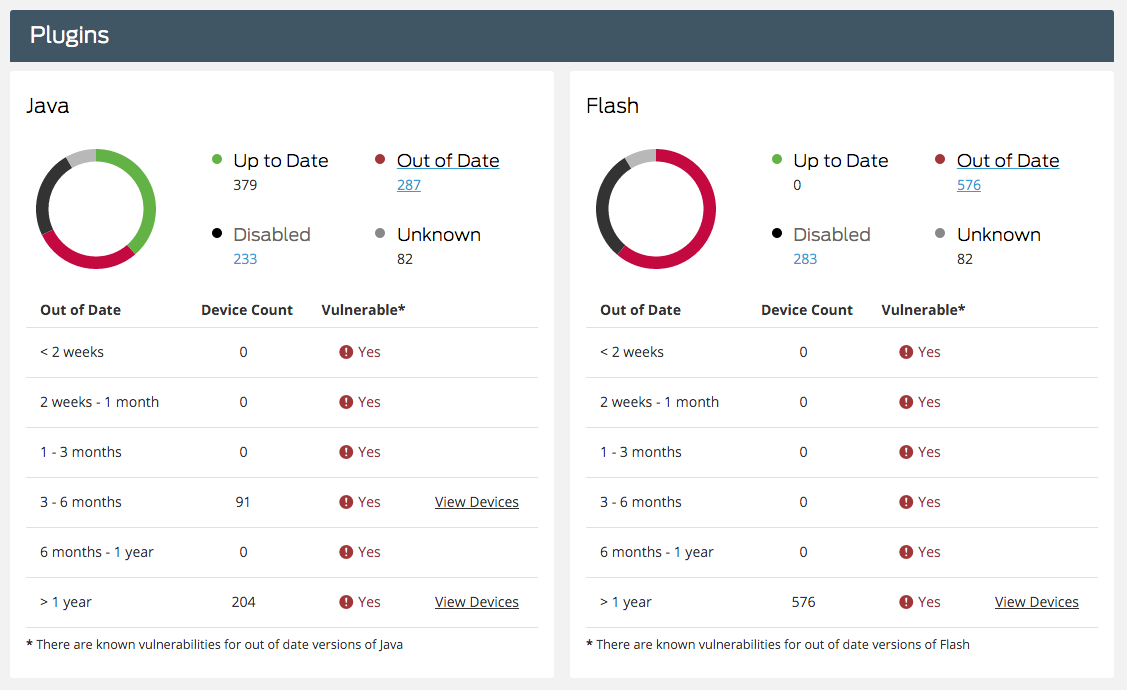
Flash Vulnerabilities & Exploits: An Information Security Primer
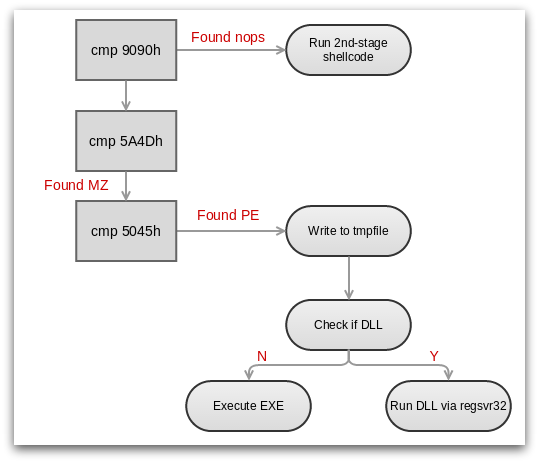
A closer look at the Angler exploit kit – Sophos News
A closer look at the Angler exploit kit – Sophos News

Untitled, PDF, Cybercrime
A closer look at the Angler exploit kit – Sophos News
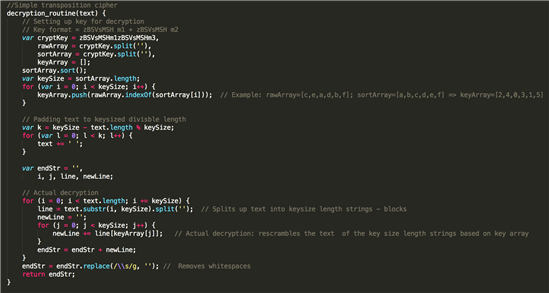
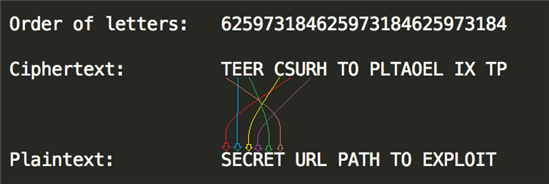
Angler Exploit Kit - Operating at the Cutting Edge