Gone Phishing: How Phishing Leads to Hacked Accounts and Identity
By A Mystery Man Writer


Gone Phishing: Everything You Need to Know About the Ever Present Threat to Your Data - Security Boulevard

Hacked Facebook accounts can take years to recover - The Washington Post
What is phishing? Examples & Prevention

How Do Websites Get Hacked?

網路釣魚如何盜帳號,冒用身分? 辨認網路釣魚四個小秘訣! – 資安趨勢部落格

Phishing - Wikipedia
What is Social Engineering?

Why Companies Shouldn't Try to Catch Employees With Fake Phishing Emails - WSJ
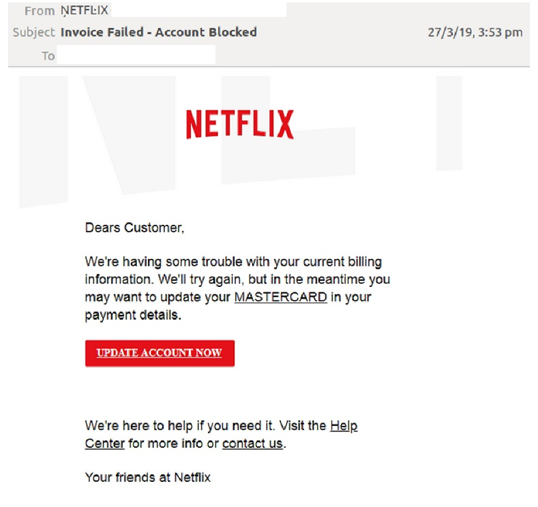
5 Ways to Detect a Phishing Email: With Examples

16 Real Examples of Business Email Compromise (BEC) Attacks